פדרו לואיס מרטין אוליברס
Former head of the financial intelligence section of the now defunct Directorate of Intelligence and Prevention Services (DISIP), now the Bolivarian Intelligence Service (SEBIN). Facing formal charges in a Florida court since 2015 for multiple counts of drug trafficking. Accused by the United States of using his position in the Venezuelan government to facilitate drug trafficking through Venezuelan airspace.
| שֵׁם | פדרו לואיס מרטין אוליברס |
| נוֹלָד | 18 באפריל, 1967 |
| מְקוֹם לֵידָה | קראקס, ונצואלה |
| תיאור (DEA) | 1.65 מ', ~113 ק"ג, שיער חום, עיניים ירוקות |
| גְמוּל | $10,000,000 (DEA) |
| סטָטוּס | התראה אדומה - האינטרפול |
| כינוי | רמון חוסה גארידו סאנצ'ס (זהות בדויה) |
רֶקַע
מרטין אוליברס, בן 51, עומד בפני כתב אישום רשמי בבית משפט בפלורידה מאז 2015 בגין מספר סעיפי סחר בסמים. בנוסף, ארצות הברית מאשימה אותו בשימוש ב"תפקידו" בממשלת ונצואלה כדי להקל על סחר בסמים דרך המרחב האווירי של ונצואלה.
The U.S. Treasury Department added a former senior official of the Bolivarian Intelligence Service (SEBIN) and two of his alleged associates to its “blacklist” of drug traffickers, along with 20 “front” companies that were used to launder illicit money.
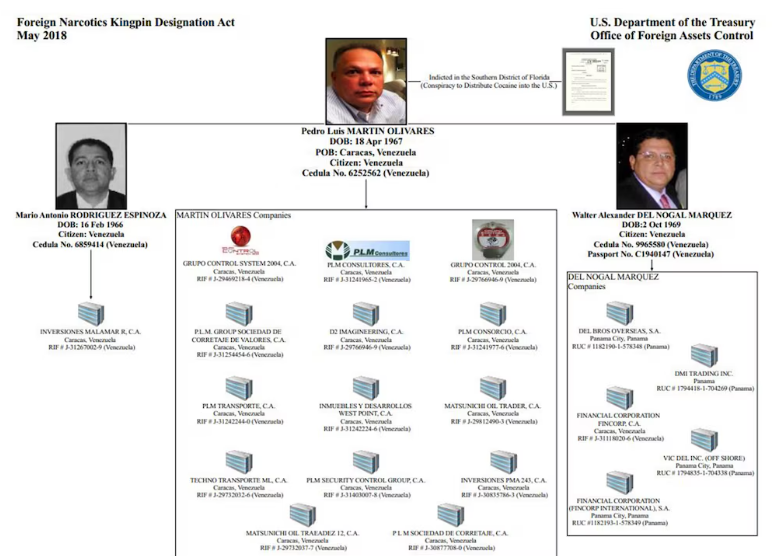
DEA רצה רישום וייעוד משרד האוצר האמריקאי
ב-29 בספטמבר 2020, מחלקת המדינה הכריזה רשמית על התגמול של 10 מיליון דולר באמצעות תוכנית התגמולים לסמים (NRP). מרטין אוליבארס רשום לצד בכירים אחרים במשטר ונצואלה.

תוכנית התגמולים לסמים של מחלקת המדינה - הודעת תגמול בסך 10 מיליון דולר
פרופיל הנושא ופרטי זיהוי
טביעת רגל דיגיטלית Discovery
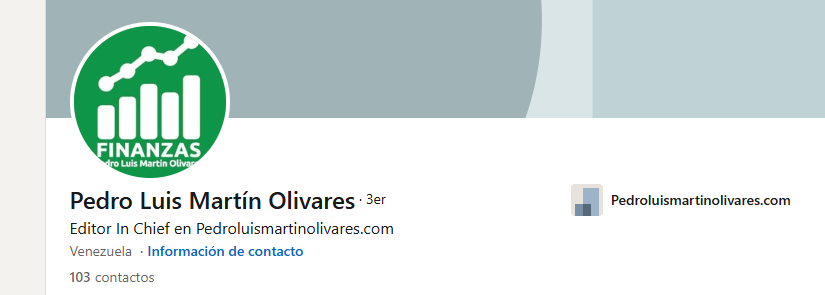
בפרופיל הלינקדאין שלו, הוא מראה כיצד הוא מנהל את האתר שלו.

עמוד אינסטגרם מקושר לנושא
ניתוח תשתית אתרים
האתר הוא התקנת וורדפרס CMS. לוח הבקרה נמצא עם ספירה בסיסית.

וורדפרס CMS מזוהה באתר האישי של הנבדק
מצא את cPanel בקלות - ספירה בסיסית
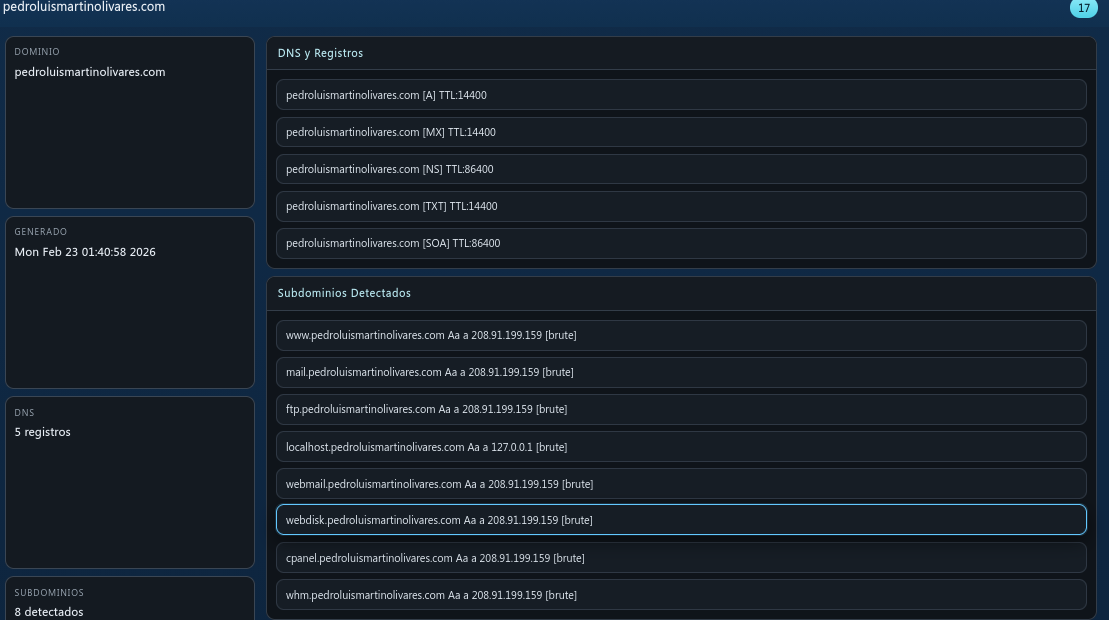
סיור תת-דומיין ו-DNS

נמצאו תת-דומיינים, מידע על DNS ורשם
פתח יציאות
מספר לא מבוטל של יציאות פתוחות התגלו בשרת
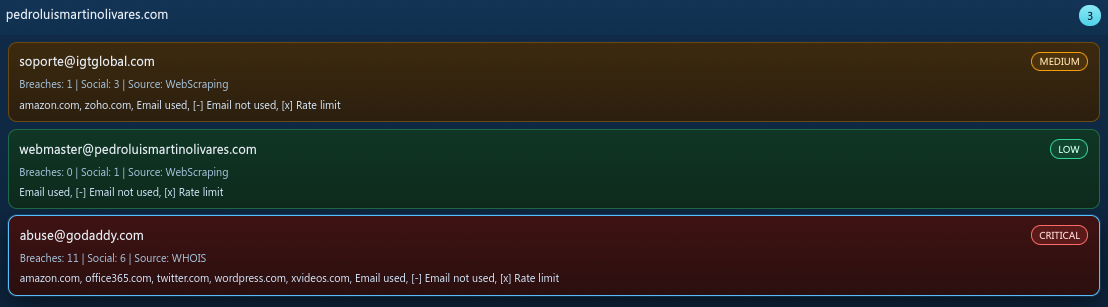
כתובות אימייל
אימיילים המשויכים לדומיין
גילוי חשבון
חשבונות המשויכים לשם המשתמש של הנבדק זוהו במספר פלטפורמות.
ממצאי פגיעות
במהלך ניתוח התשתית התגלו מספר CVEs וחשיפות שירות:
| חוּמרָה | CVE / מזהה | שֵׁרוּת | תֵאוּר |
|---|---|---|---|
| מידע | mysql-info | אינטרנט | [mysql-info] [javascript] [מידע] |
| מידע | snmpv3-detect | אינטרנט | [snmpv3-detect] [javascript] [מידע] |
| מידע | imap-detect | אינטרנט | [imap-detect] [tcp] [מידע] |
| מידע | mysql-detect | אינטרנט | [mysql-detect] [tcp] [מידע] |
| מידע | pop3-זיהוי | אינטרנט | [pop3-detect] [tcp] [מידע] |
| מידע | mysql-native-password | אינטרנט | [mysql-native-password] [tcp] [מידע] |
| מידע | tls-גרסת | אינטרנט | [tls-version] [ssl] [מידע] |
| מידע | tls-גרסת | אינטרנט | [tls-version] [ssl] [מידע] |
| מידע | spf-record-detect | אינטרנט | [spf-record-detect] [dns] [מידע] |
| מידע | txt-טביעת אצבע | אינטרנט | [txt-fingerprint] [dns] [מידע] |
| מידע | caa-טביעת אצבע | אינטרנט | [caa-fingerprint] [dns] [מידע] |
| מידע | שרת שמות-טביעת אצבע | אינטרנט | [שרת שמות-טביעת אצבע] [dns] [מידע] |
| מידע | mx-טביעת אצבע | אינטרנט | [mx-fingerprint] [dns] [מידע] |
| מידע | ssl-מוציא | אינטרנט | [ssl-מוציא] [ssl] [מידע] |
| מידע | ssl-dns-names | אינטרנט | [ssl-dns-names] [ssl] [מידע] |
| מידע | wildcard-tls | אינטרנט | [wildcard-tls] [ssl] [מידע] |
ניסיון גישה למסד נתונים
בעת ניסיון להיכנס למסד הנתונים MySQL של השרת, החיבור נאסר על ידי מערכת מניעת החדירה של המארח.
חיבור נאסר על ידי שרת IPS בעת ניסיון גישה למסד הנתונים של MySQL
בהפקה
החקירה הזו נמשכת. ממצאים נוספים, ניתוח תשתיות מעמיק יותר ומודיעין מאשש יפורסמו עם התקדמות החקירה.
הערת החוקר
This report is based entirely on open-source intelligence (OSINT). No classified information was accessed. No confidential sources were used. Everything documented here is publicly available — if you know where to look.
