Pedro Luis Martín Olivares
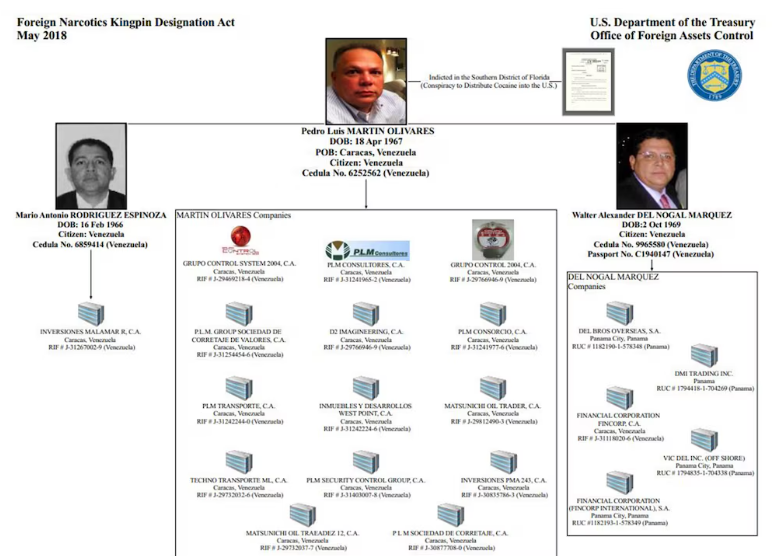
Exjefe de la sección de inteligencia financiera de la extinta Dirección de Inteligencia y Servicios de Prevención (DISIP), ahora Servicio Bolivariano de Inteligencia (SEBIN). Enfrenta cargos formales en un tribunal de Florida desde 2015 por múltiples cargos de narcotráfico. Acusado por Estados Unidos de usar su posición en el governo venezuelano para facilitar el narcotráfico a través del espacio aéreo venezolano.
| Nombre | Pedro Luis Martín Olivares |
| Nacimiento | April 18, 1967 |
| Lugar de nacimiento | Caracas, Venezuela |
| Descripción (DEA) | 1.65 m, ~113 kg, Cabello castaño, ojos verdes |
| Recompensa | $10,000,000 (DEA) |
| Estado | Alerta Vermelho — Interpol |
| Álias | Ramón José Garrido Sánchez (Identidad falsa) |
Contexto
Martín Olivares, 51 anos, enfrenta acusações formais num tribunal da Flórida desde 2015 por diversas acusações de tráfico de drogas. Além disso, os Estados Unidos acusam-no de usar a sua “posição” no governo venezuelano para facilitar o tráfico de drogas através do espaço aéreo venezuelano.
The U.S. Treasury Department added a former senior official of the Bolivarian Intelligence Service (SEBIN) and two of his alleged associates to its “blacklist” of drug traffickers, along with 20 “front” companies that were used to launder illicit money.
DEA queria listagem e designação do Departamento do Tesouro dos EUA
Em 29 de setembro de 2020, o Departamento de Estado anunciou oficialmente a recompensa de US$ 10 milhões por meio do Programa de Recompensas de Narcóticos (NRP). Martín Olivares está listado ao lado de outros altos funcionários do regime venezuelano.

Programa de Recompensas de Narcóticos do Departamento de Estado – anúncio de recompensa de US$ 10 milhões
Perfil do sujeito e detalhes de identificação
Descubrimiento de huella digital
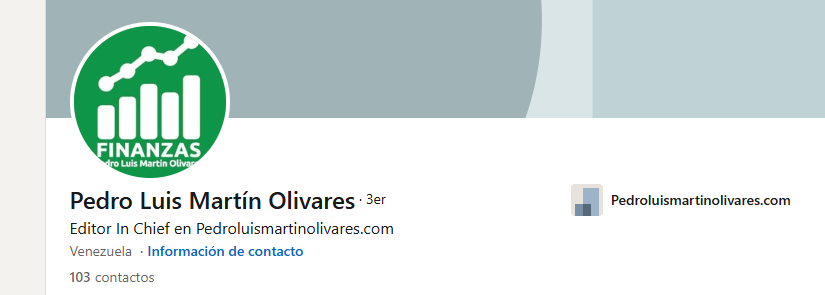
En su perfil de LinkedIn, muestra cómo gestiona su propio sitio web.

Página do Instagram vinculada ao assunto
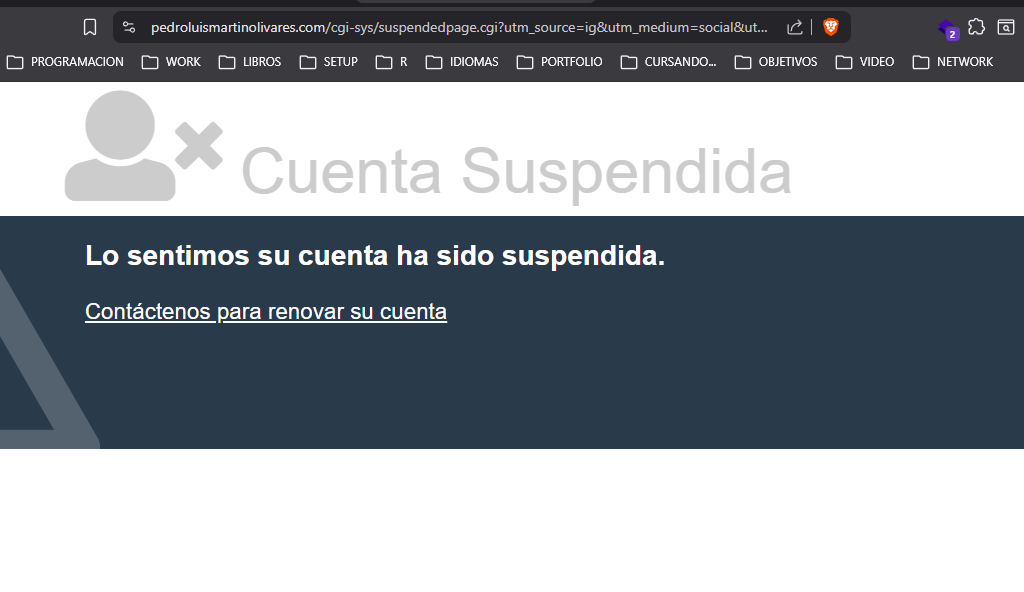
Analise de infraestrutura do site
O site e uma instalacao de CMS WordPress. O painel de controle foi encontrado com enumeracao basica.

CMS WordPress identificado no site pessoal do sujeito
Encontrei o cPanel com facilidade – enumeração básica
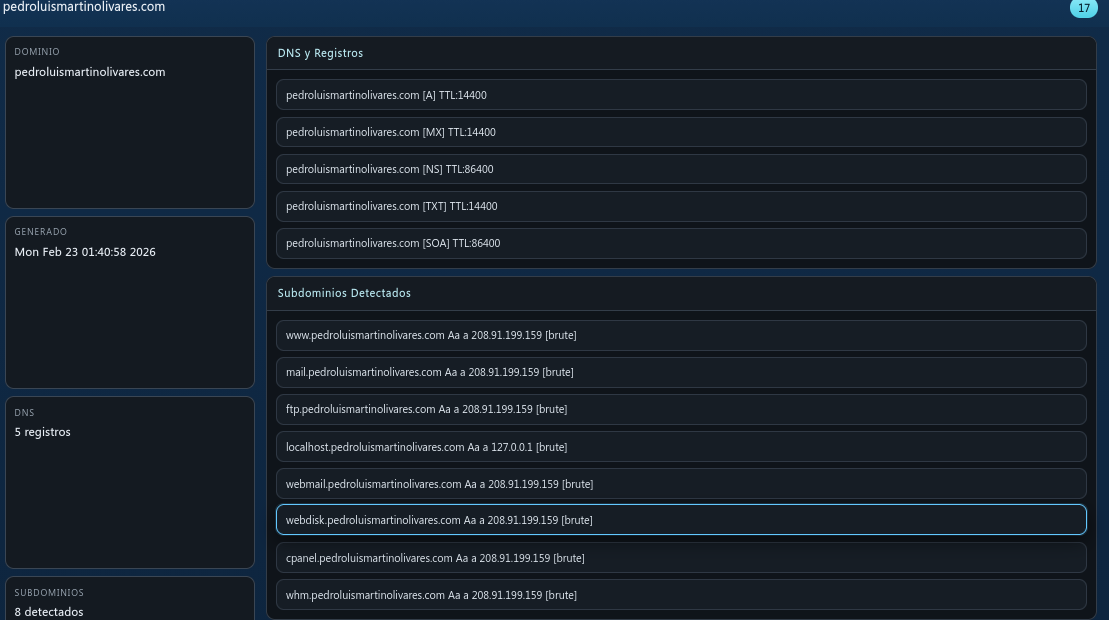
Reconocimiento de subdominios y DNS

Subdomínios encontrados, informações de DNS e registrador
Puertos abiertos
Um número significativo de portas abertas descobertas no servidor
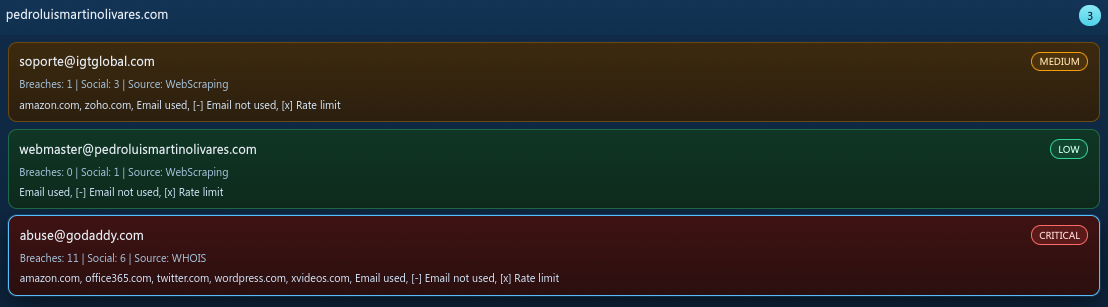
Direcciones de correo electrónico
E-mails associados ao domínio
Descubrimiento de cuentas
Foram identificadas contas associadas ao nome de usuario do sujeito em multiplas plataformas.
Hallazgos de vulnerabilidades
Se descubrieron numerosos CVEs y exposiciones de servicios durante el análisis de infraestrutura:
| Severidad | CVE / ID | Servicio | Descripción |
|---|---|---|---|
| INFO | mysql-info | web | [mysql-info] [javascript] [info] |
| INFO | snmpv3-detect | web | [snmpv3-detect] [javascript] [info] |
| INFO | imap-detect | web | [imap-detect] [tcp] [info] |
| INFO | mysql-detect | web | [mysql-detect] [tcp] [info] |
| INFO | pop3-detect | web | [pop3-detect] [tcp] [info] |
| INFO | mysql-native-password | web | [mysql-native-password] [tcp] [info] |
| INFO | tls-version | web | [tls-version] [ssl] [info] |
| INFO | tls-version | web | [tls-version] [ssl] [info] |
| INFO | spf-record-detect | web | [spf-record-detect] [dns] [info] |
| INFO | txt-fingerprint | web | [txt-fingerprint] [dns] [info] |
| INFO | caa-fingerprint | web | [caa-fingerprint] [dns] [info] |
| INFO | nameserver-fingerprint | web | [nameserver-fingerprint] [dns] [info] |
| INFO | mx-fingerprint | web | [mx-fingerprint] [dns] [info] |
| INFO | ssl-issuer | web | [ssl-issuer] [ssl] [info] |
| INFO | ssl-dns-names | web | [ssl-dns-names] [ssl] [info] |
| INFO | wildcard-tls | web | [wildcard-tls] [ssl] [info] |
Intento de acceso a base de datos
Ao tentar iniciar sessao no banco de dados MySQL do servidor, a conexao foi bloqueada pelo sistema de prevencao de intrusoes do host.
Conexão banida pelo servidor IPS ao tentar acessar o banco de dados MySQL
En producción
Esta investigacao esta em andamento. Descobertas adicionais, analise de infraestrutura mais profunda e inteligencia corroborativa serao publicadas a medida que a investigacao avancar.
Nota do pesquisador
Este relatorio baseia-se inteiramente em inteligencia de fontes abertas (OSINT). Nenhuma informacao classificada foi acessada. Nenhuma fonte confidencial foi utilizada. Tudo documentado aqui esta disponivel publicamente — se voce sabe onde procurar.
