Pedro Luis Martín Olivares
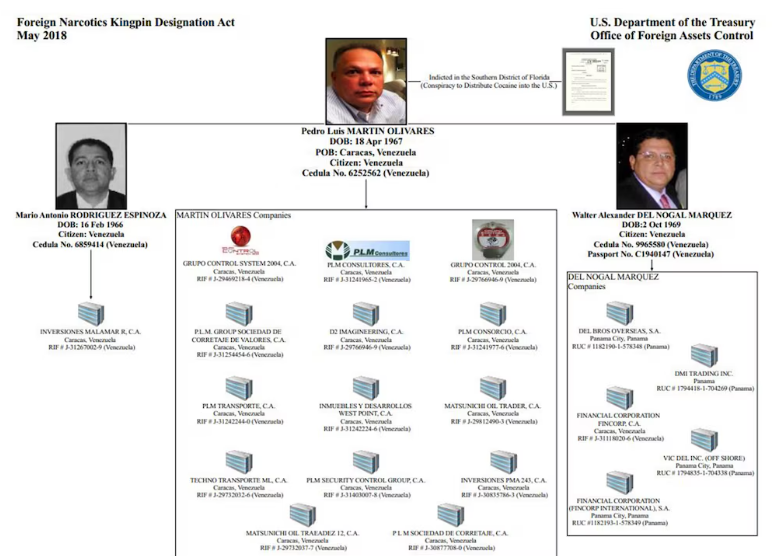
Former head of the financial intelligence section of the now defunct Directorate of Intelligence and Prevention Services (DISIP), now the Bolivarian Intelligence Service (SEBIN). Facing formal charges in a Florida court since 2015 for multiple counts of drug trafficking. Accused by the United States of using his position in the Venezuelan government to facilitate drug trafficking through Venezuelan airspace.
| Name | Pedro Luis Martín Olivares |
| Born | April 18, 1967 |
| Place of Birth | Caracas, Venezuela |
| Description (DEA) | 1.65 m, ~113 kg, Brown Hair, Green Eyes |
| Reward | $10,000,000 (DEA) |
| Status | Red Alert — Interpol |
| Alias | Ramón José Garrido Sánchez (False identity) |
Background
Martín Olivares, 51, has been facing formal charges in a Florida court since 2015 for several counts of drug trafficking. In addition, the United States accuses him of using his “position” in the Venezuelan government to facilitate drug trafficking through Venezuelan airspace.
The U.S. Treasury Department added a former senior official of the Bolivarian Intelligence Service (SEBIN) and two of his alleged associates to its “blacklist” of drug traffickers, along with 20 “front” companies that were used to launder illicit money.
DEA wanted listing and U.S. Treasury Department designation
On September 29, 2020, the State Department officially announced the $10 million reward through the Narcotics Rewards Program (NRP). Martín Olivares is listed alongside other senior officials of the Venezuelan regime.

State Department Narcotics Rewards Program — $10 million reward announcement
Subject profile and identification details
Digital Footprint Discovery
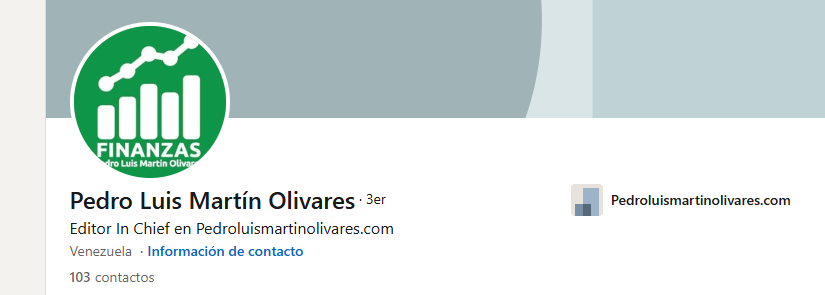
On his LinkedIn profile, he shows how he manages his own website.

Instagram page linked to the subject
Website Infrastructure Analysis
The site is a CMS WordPress installation. The control panel was found with basic enumeration.

WordPress CMS identified on the subject's personal website
Found the cPanel with ease — basic enumeration
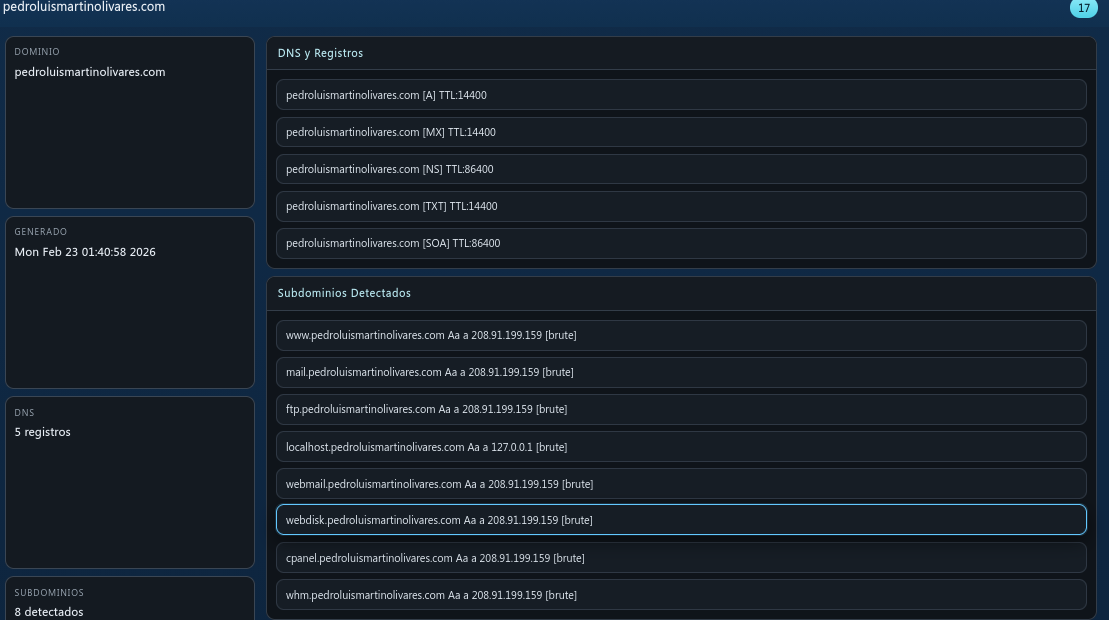
Subdomain and DNS Reconnaissance

Subdomains found, DNS and registrar information
Open Ports
A significant number of open ports discovered on the server
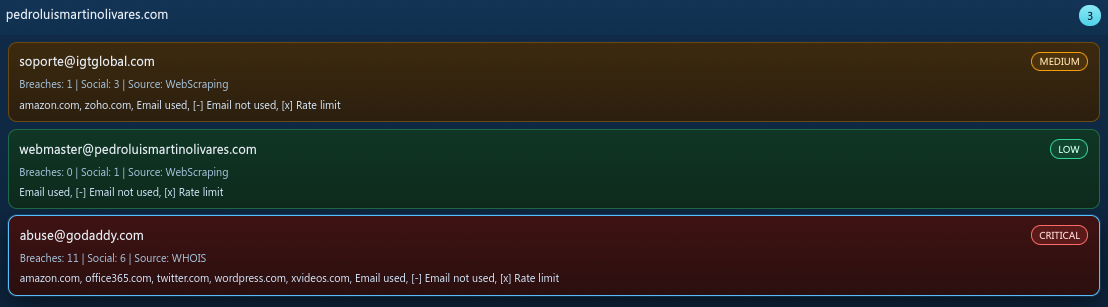
Email Addresses
Emails associated with the domain
Account Discovery
Accounts associated with the subject's username were identified across multiple platforms.
Vulnerability Findings
Numerous CVEs and service exposures were discovered during the infrastructure analysis:
| Severity | CVE / ID | Service | Description |
|---|---|---|---|
| INFO | mysql-info | web | [mysql-info] [javascript] [info] |
| INFO | snmpv3-detect | web | [snmpv3-detect] [javascript] [info] |
| INFO | imap-detect | web | [imap-detect] [tcp] [info] |
| INFO | mysql-detect | web | [mysql-detect] [tcp] [info] |
| INFO | pop3-detect | web | [pop3-detect] [tcp] [info] |
| INFO | mysql-native-password | web | [mysql-native-password] [tcp] [info] |
| INFO | tls-version | web | [tls-version] [ssl] [info] |
| INFO | tls-version | web | [tls-version] [ssl] [info] |
| INFO | spf-record-detect | web | [spf-record-detect] [dns] [info] |
| INFO | txt-fingerprint | web | [txt-fingerprint] [dns] [info] |
| INFO | caa-fingerprint | web | [caa-fingerprint] [dns] [info] |
| INFO | nameserver-fingerprint | web | [nameserver-fingerprint] [dns] [info] |
| INFO | mx-fingerprint | web | [mx-fingerprint] [dns] [info] |
| INFO | ssl-issuer | web | [ssl-issuer] [ssl] [info] |
| INFO | ssl-dns-names | web | [ssl-dns-names] [ssl] [info] |
| INFO | wildcard-tls | web | [wildcard-tls] [ssl] [info] |
Database Access Attempt
When trying to log in to the MySQL database of the server, the connection was banned by the host's intrusion prevention system.
Connection banned by server IPS when attempting MySQL database access
In Production
This investigation is ongoing. Additional findings, deeper infrastructure analysis, and corroborating intelligence will be published as the investigation progresses.
Investigator's Note
This report is based entirely on open-source intelligence (OSINT). No classified information was accessed. No confidential sources were used. Everything documented here is publicly available — if you know where to look.
